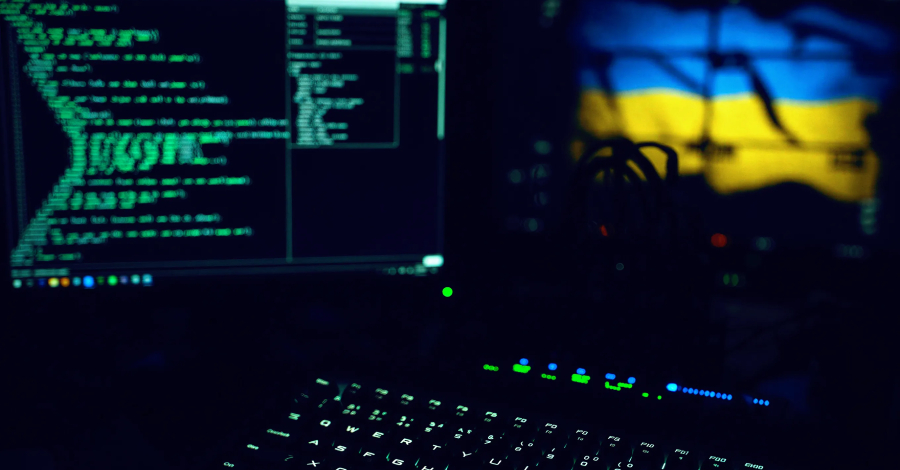
Google: Half of 2025’s 90 Exploited Zero-Days Aimed at Enterprises
Less than half of the total zero-days have been attributed to a threat actor, but spyware vendors and China are in the lead. The post Google: Half of 2025’s 90 Exploited Zero-Days Aimed at Enterprises appeared first on SecurityWeek. Source: https://www.securityweek.com/google-half-of-2025s-90-exploited-zero-days-aimed-at-enterprises/
Google: Half of 2025’s 90 Exploited Zero-Days Aimed at Enterprises Read More »
Cybersecurity