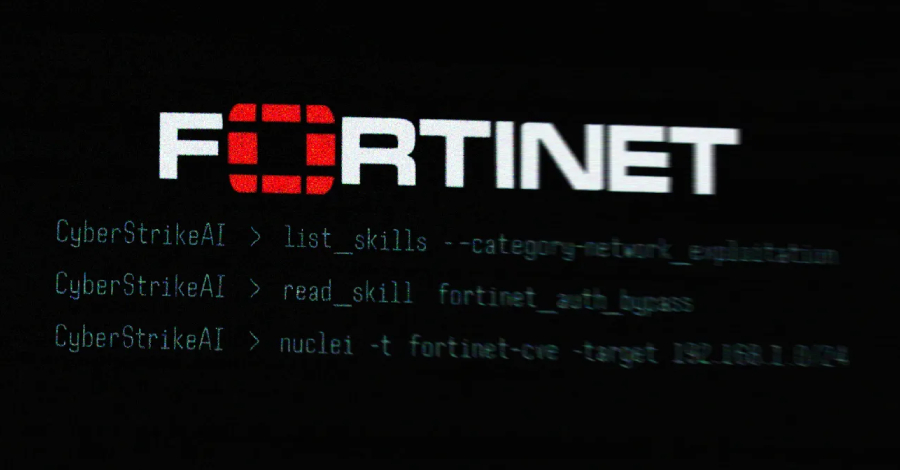
Open-Source CyberStrikeAI Deployed in AI-Driven FortiGate Attacks Across 55 Countries
The threat actor behind the recently disclosed artificial intelligence (AI)-assisted campaign targeting Fortinet FortiGate appliances leveraged an open-source, AI-native security testing platform called CyberStrikeAI to execute the attacks. The new findings come from Team Cymru, which detected its use following an analysis of the IP address (“212.11.64[.]250”) that was used by the suspected Source: https://thehackernews.com/2026/03/open-source-cyberstrikeai-deployed-in.html
Open-Source CyberStrikeAI Deployed in AI-Driven FortiGate Attacks Across 55 Countries Read More »
Cybersecurity